The 1.0.0-beta version of the Azure SDK for java introduces a new model for authenticating that is called “file-based authentication”. Although being described as an experimental feature, it is a way to use a service principal account when managing ARM-based resources in Azure.
Creating a Service Principal
The documentation for setting this up is tucked away in a file named AUTH.md in github, but you have to know a little Azure AD in order to understand what is happening here. In step 5. you create the service principal via the Azure CLI command below
azure config mode arm azure ad sp create --name spFawltytowers2 --password <pwd>
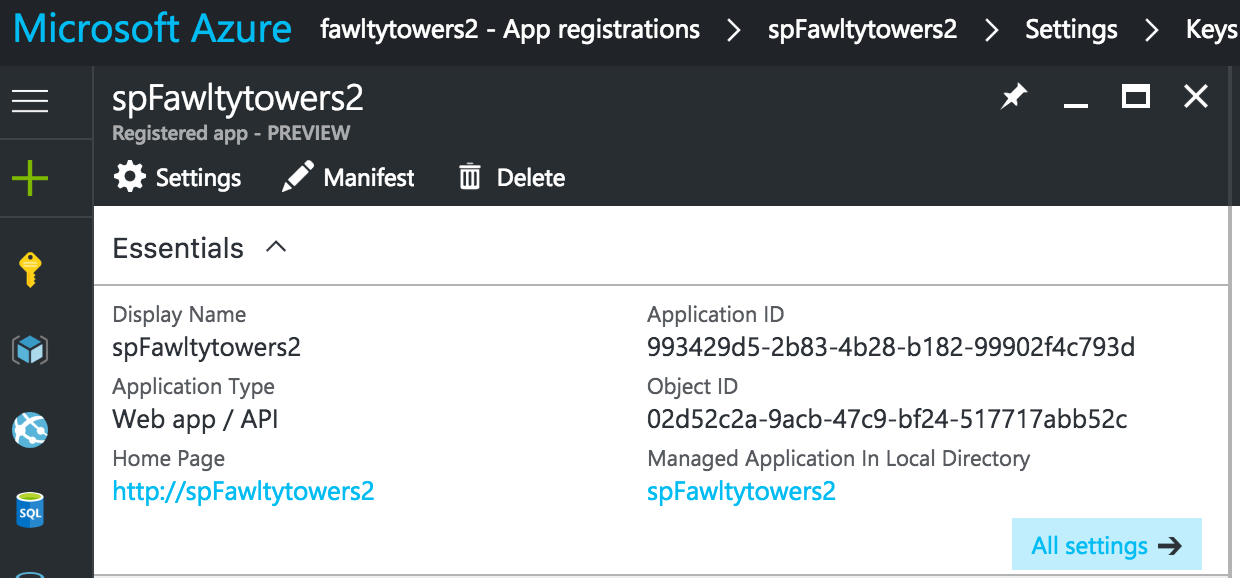
This Service Principal shows up as an application in the Azure Portal which is a little confusing since it is listed amongst real application entries. The guid of the the Application ID is something you need to copy, because you will use this as the client id in your Java program configuration.
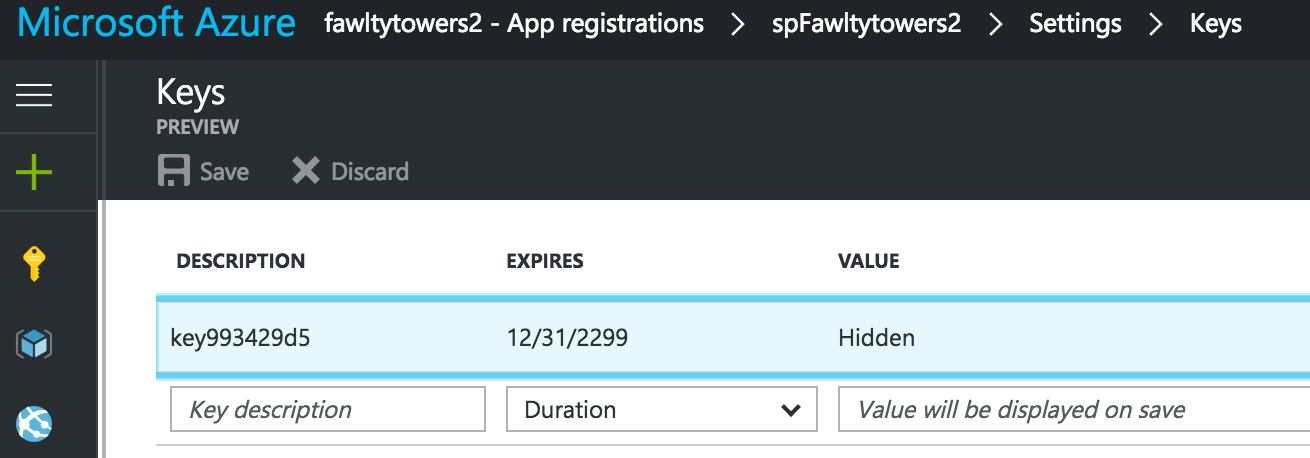
Even though you did provide a password, you need to create a key in the portal. The value can be anything you like but make sure you don’t loose it, because the portal will not display its value once you have saved it.
Creating the configuration file
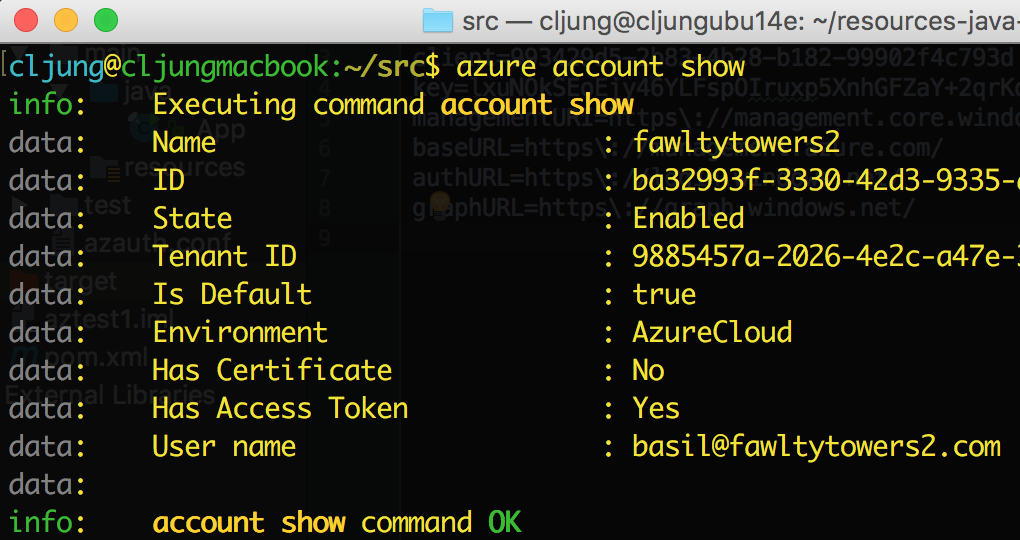
The configuration file holds the client + key to identify the service principal but it should also contain information about the Azure subscription that we like to use and the Azure AD that can authenticate us. The Azure CLI command “azure account show” can display your current subscription and AAD tenant. The ID field is the subscription ID and you also need to copy the Tenant ID, which is the guid for the Azure AD that we will authenticate with.
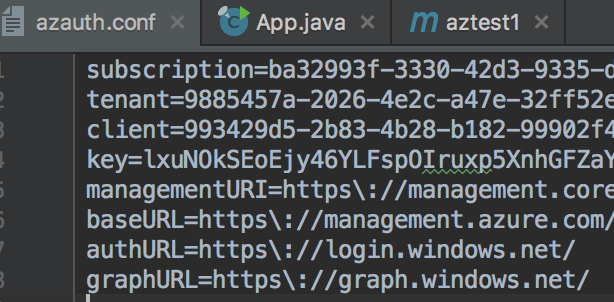
These four values – client, key, subscription id and tenant id – is something you put in a text file you store with your Java application. It has the following format:
The URLs is something you likely just can steal with pride from somewhere, but if you really like to get the values for real, you can get them with the Azure CLI command “azure account env show AzureCloud”, where the value “AzureCloud” comes of the output in the previous CLI command.
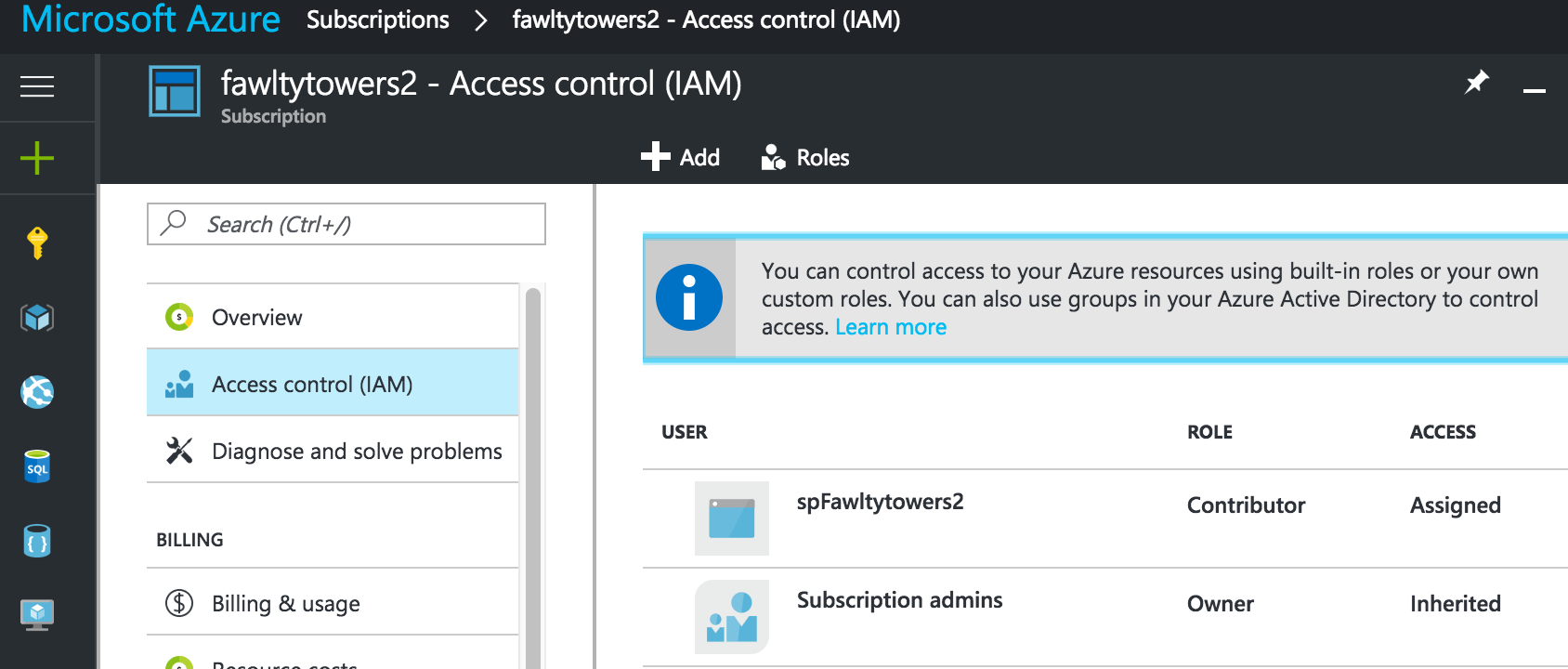
Granting access to the Service Principal
If you ran your Java program now, it would be able to authenticate against Azure AD using the Service Principal but it would not be able to do anything in the Azure Subscription because we haven’t granted it any access rights yet. Depending on how you are going to use this service principal, you may add it to a resource group, etc, but if you are building something that should be able to manage all resources in the subscription, you need to add it as a Contributor to the entire subscription.
Go to Subscriptions (Yellow key) > Access >Control (IAM) and add the service principal as a Contributor.
Testing that it works
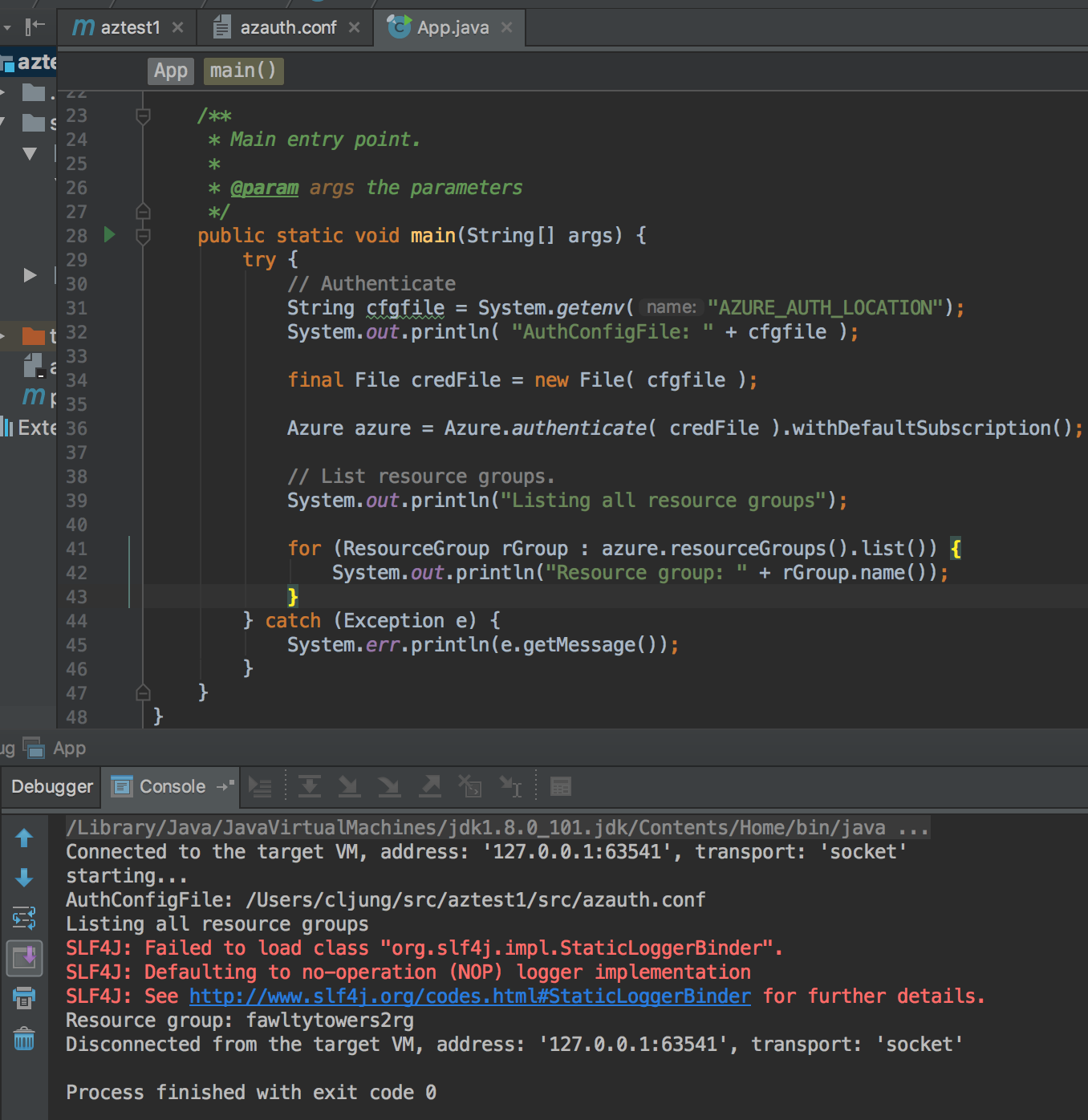
To test that it works you can create a tiny Java application that uses the Azure SDK for Java. The 1.0.0-beta version of the SDK builds with Maven, so create a Maven project and enter the dependancy in the pom.xml file
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<groupId>com.fawltytowers2</groupId>
<artifactId>aztest1</artifactId>
<version>1.0-SNAPSHOT</version>
<dependencies>
<dependency>
<groupId>com.microsoft.azure</groupId>
<artifactId>azure</artifactId>
<version>1.0.0-beta3</version>
</dependency>
</dependencies>
</project>
Then pass the configuration file to the Azure.authenticate method and you will be able to access resources in your subscription. The below little sample program just lists all resource groups (which in this test was just a single one)
References
Azure SDK for Java
https://github.com/Azure/azure-sdk-for-java
Documentation for creating the Service Principal
https://github.com/Azure/azure-sdk-for-java/blob/master/AUTH.md
Sample Java program for testing
https://github.com/Azure-Samples/resources-java-manage-resource-group