This post is also about data ingestion to Blob Storage using a SAS-Token. But if the previous showed how you could create a SAS-Token just-in-time to upload a file via a web browser, this post covers the scenario where you want to lock down upload rights to a specific ip address or range of ip addresses. It might be a B2B scenario or a mobile unit uploading data from somewhere in the field.
Generating the SAS-token with IP address range
It is really quite simple to lock the SAS-Token to a certain ip range. You just use one of the overlapped methods of GetSharedAccessSignature that takes the IPAddressOrRange object as the last parameter. The IPAddressOrRange takes a from-to addres range, which means you have to specify it as 11.22.33.41 and 11.22.33.49 if that is the range you want.
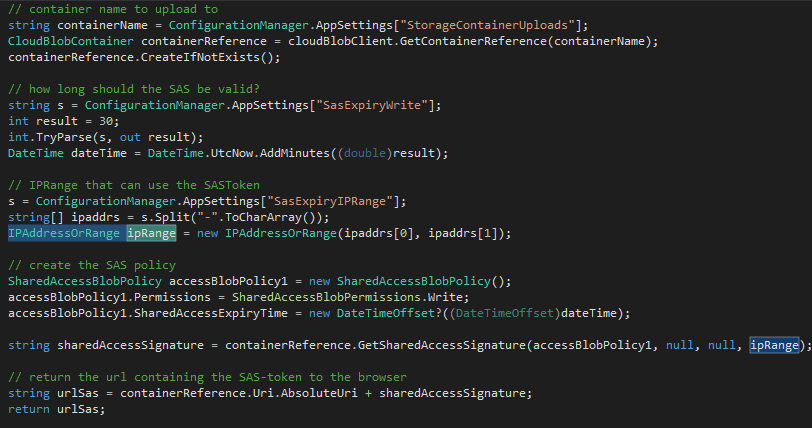 In the above example, the SAS-Token is generated on the Container level with permission to Write for a certain amount of time, so that the sending application can upload files to this container.
In the above example, the SAS-Token is generated on the Container level with permission to Write for a certain amount of time, so that the sending application can upload files to this container.
The generated url must be passed on and perhaps stored in a config file in the sending application.
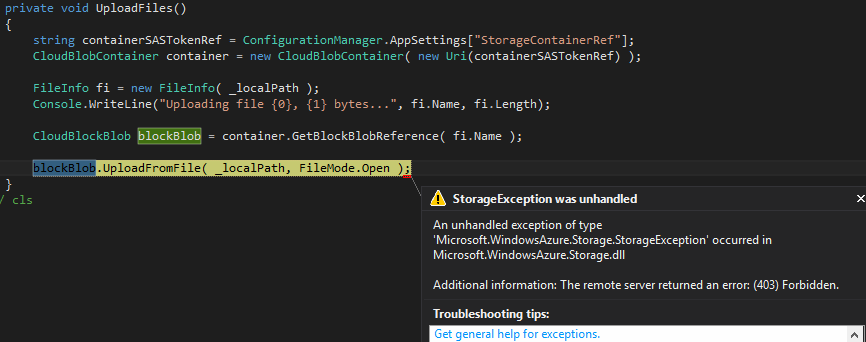
Using the SAS-token to upload files
Since you only have a SAS-Token for a Container and not the key to the Storage Account, you have to work directly with the Container when you upload files. The code to upload a file is really just a few lines. The SAS-Token is read from the config file and we grab access to the Container using it. The GetBlockBlobReference names the blob and gives us a reference to where we would like to upload it to.
If you try to do this from an ip address that is not in the allowed range, the upload will fail with a HTTP 403 Forbidden status code.
Summary
This technique is publically documented but yet suprisingly many people I’ve met do not know it and therefor say that you can’t limit who can upload files to an Azure Storage Container. Generating a SAS-Token with the IPAddressOrRange specifies may be just what you are looking for since it retricts access to ip addresses.
References
MSDN Documentation for GetSharedAccessSignature
https://msdn.microsoft.com/en-us/library/azure/mt616570.aspx
SharedAccessSignature – documentation
https://azure.microsoft.com/en-us/documentation/articles/storage-dotnet-shared-access-signature-part-1/
…